A great product? Check. Awesome workflows? Check. Security? Can you check this item from your list? If not, this article is for you. As companies develop applications and go from one stage of a product lifecycle to the other, security gains prominence. Development, integration, testing, implementation, deployment, delivery – It is important to ensure security across all the stages. This will help companies keep pace with the rapid software updates and product releases in an efficient manner. Security issues can be addressed in a more proactive manner, and they are often easier, faster and cheaper to fix. The new approach – DevSecOps – is thus important. It stands for development, security and operations and puts security at the heart of an application strategy.
Ready to protect your app?
Start 30-days FREE TRIAL. No credit card required. Deliver Secure Mobile Apps Faster in minutes with the leader in application security.

DevSecOps
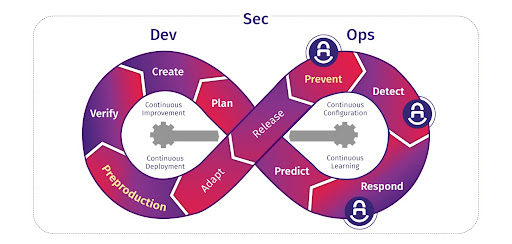
DevSecOps as a concept believes in the placement of security at the intersection of development and operations. It helps integrate security objectives in the early stages of the software development lifecycle. The responsibility and ownership of security lie with all team members at every stage. It leverages automation to ensure that unstable, non-compliant or unsecure code doesn’t creep into an application.
Source: Synk
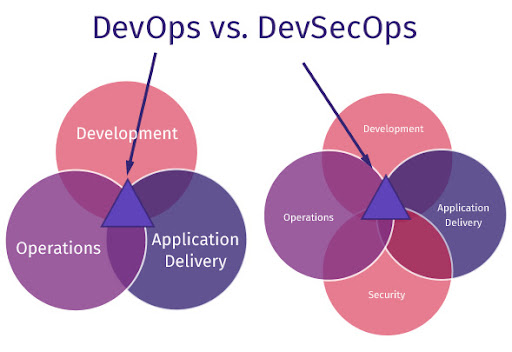
DevSecOps Vs DevOps
DevOps focuses on shared responsibility between development and operations functions. DevSecOps extends it further by adding the element of security to be in line with the recent needs of software applications. Security thus becomes an important part in the software development lifecycle. So teams can expect activities focused on enhancing application security to be looked at right from the beginning of a project. The end result is a lot more secure, robust application as compared to what a DevOps strategy might have initially set out to achieve.
Source: Code Dx
DevSecOps Benefits
The first and foremost benefit of DevSecOps is that security is seen to be everybody’s responsibility. This ensures that security is an in-built feature rather than an afterthought. Applications can thus be developed faster and delivered on time.
Usually fixing security issues can be a time-consuming and costly affair. But here, fixing issues is more rapid. Since issues can be identified during the earlier stages of the SDLC, it is also cheaper to fix them. Time delays are reduced, and issues are fixed as they are identified. Compliance is simplified and vulnerability patching is more rapid. This means an improved security posture.
Automated test suites are used to ensure more robust features. Frequent iterative advancements are seen leading to an overall improved upgraded security level. Thus, as applications go digital and open up to more people, security practices follow a repeatable, adaptive process and also help companies stay a step ahead of attackers. Leadership teams can thus focus on enhancing their business while safely allowing their customers to transact with them.
DevSecOps Best Practices
DevSecOps requires a major shift in thinking and strategy. Teams need to be aligned in order to ensure that maximum benefits are leveraged from this principle right from the beginning of a project. A couple of best practices to follow are:
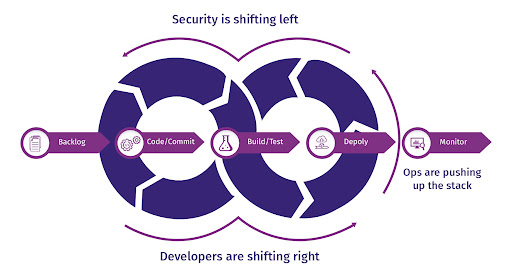
Adopt a ‘Shift Left’ Approach
Rather than thinking about security towards the end (right), the application strategy here pushes security to the beginning (left). This means including the relevant stakeholders like cybersecurity experts and testing the relevant security loopholes right from the beginning. All security gaps should be reported, tested and fixed.
Get your Basics Right
Secure coding practices, incident management, a dedicated security team and clearly documented compliance requirements are a must irrespective of the application being developed. Setting standards and policies also help.
Incorporate a Culture of Security Across the Teams
Companies should ensure that engineers, developers, architects, testers, project managers, operations and security experts come together to chart out features and testing plans so that security features as an important element throughout the cycle of a project/application. Developers should be trained to develop code that is both error free and secure to get a final go-ahead from their team leaders. Security mandates should be followed by all.
Transfer Knowledge
Regular sessions with team members will ensure that they know why security is important. It is also a good idea to make developers think like attackers and replicate real-life scenarios. Developers and testers often focus a lot on testing and improving the product features with security testing usually undertaken at the last minute in a hurry. But teams should be given a clear mandate to develop secure applications.
Have Regular Audits
Teams should be encouraged to minimize bugs and ensure secure codes. Audits should be conducted regularly with proper documentations and follow-ups. Relevant alerts should be given when thresholds are passed and teams should be held accountable for fixing such issues.
DevSecOps Myths
DevSecOps is somewhat like the word ‘digitization’. Everyone talks about it but few know what it actually means. Many people misunderstand it and use the word just to look good in front of their peers. The same holds true for DevSecOps which, to many, is a mystery. Let us bust a few of the myths associated with it:
You need extremely talented, senior developers for DevSecOps
DevSecOps requires a security-focused approach and not really ninja level coding skills. If you are able to train your people well and make them work towards focusing on improving security of your applications, you already have a great start. Of course, having a cyber security expert in the team helps, but you do not necessarily need to go for a separate, niche team.
You have to choose between DevSecOps and Agile
You do not have to do this. They go hand in hand and foster collaboration amongst team members. Agile could apply to concepts beyond security and help application development more robust and well planned. DevSecOps focuses on security methodologies and tools which make the application more secure.
You can buy DevSecOps
No matter what people tell you, this never works out. As mentioned earlier, DevSecOps is a methodology which helps teams work towards securing their applications in a more proactive manner right from the early stages. Buying a ‘DevSecOps package’ can never work out as your teams will never be able to imbibe the culture of security if you try to outsource it to some random team.
DevSecOps predominantly focuses on speed
Agreed that DevSecOps helps take applications faster to the market as teams will not have to sit and fix security issues at the last minute. But, the focus here is not speed. It is security. Automation does help fasten the time to identify and fix issues, but the essence of this exercise is to develop applications that are robust and safer to use.
DevSecOps and remote work can’t go hand-in-hand
Just as we have all learned to work flawlessly by being connected remotely, DevSecOps too can be implemented remotely. It is just like any other training programme that teams take to improve their software development and testing practices. A remote working model can’t get in its way.
A step-by-step guide to implementing DevSecOps
Implementing DevSecOps needs a well-thought-through strategy. We are outlining 8 key steps to successfully implement a DevSecOps strategy that will work:
-
Planning:
This is the first and most important step to understand what all will be covered and how long it will take to implement security features and test criteria. Different threat models can be considered here.
-
Development:
As they say, well begun is half done. Since your application is only as secure as your base code, developing and implementing secure coding practices becomes paramount. A code review system might help so everybody can pool in with their ideas. This will also ensure uniformity, best practices and standardized codes.
-
Building:
Here, automated build tools can help. Source code can be then combined with the machine code. These tools can also help replace any unsecure code with more robust codes from the resource library.
-
Testing:
This again is an important step where teams need to ensure that different test cases are created. Real life scenarios can also be tested through automated testing frameworks.
-
Deployment:
Here the application is deployed for user testing
-
Operation:
Here, zero-day threats are evaluated and fixed in a periodic fashion
-
Monitoring:
This step ensures that the application and its different components are checked on a regular basis for any vulnerabilities. This will ensure that the application runs as expected.
-
Scaling:
As the application adds more features or reaches out to more people, data needs to be secured. Companies no longer have to depend on large data centers to maintain confidential information. They can simply scale their IT infrastructure.
Challenges with DevSecOps
Teams have their own deadlines to meet. When developers and testers are asked to keep a check on security, they see it as an additional item to be ticked from their list. This could of course mean additional effort or even delays. DevSecOps becomes a baggage for many in this way. This is where support from the top management really helps. A shift from the “this is how we have been doing” mentality is always difficult. Developers and security professionals come together often leading to some clashes in their thought processes and priorities. A good project manager in such situations has to keep both parties happy while ensuring that a robust, secure application gets released. Silos can creep up too. Hence regular catch ups and team meetings help. Another challenge is the dearth of talent in some companies. Many companies do not have good cyber security professionals who can help steer the project in the right direction. This position is important and needs special treatment and place in the organization.
Tools to help implement DevSecOps smoothly
Many tools are available to help check for security and compliance of applications. A few of them are:
Static application security testing (SAST)
This helps teams check for vulnerabilities in their own proprietary code. It can also be automated and helps detect security gaps early on in the product SDLC.
Software composition analysis (SCA)
Here, open-source components of a code are checked. License compliance and security vulnerabilities are managed and monitored continuously. Specific policy enforcement practices are also observed at times to limit the download or transfer of files, binaries or builds.
Dynamic and Interactive Application Security Testing (DAST and IAST)
Here, a running application’s exposed interfaces are tested for flaws or loopholes.
Container runtime security
This approach tests applications during runtime by leveraging behavioural analytics.
Final Thoughts
Thus as we saw above, just developing cool applications is not enough in today’s time and age. Security needs to be given equal importance. Armed with the DevSecOps methodology, companies can ensure that their applications are robust, safe and perfect to be used by their customers. Runtime application self-protection (RASP) can be looked at too when it comes to checking for threats and vulnerabilities while an application is running. Runtime threats are thereby quicker to fix with this strategy. They can help monitor an application continuously for any unusual behaviour or interaction with other applications. Configurations and settings are rapidly checked too. We are happy to help give further details if this sounds interesting to you. Contact us today.
Frequently Asked Questions
1. Is DevSecOps the same as cybersecurity?
Cybersecurity involves a lot of domains whereas DevSecOps is just a part of cybersecurity. DevSecOps stands for Development, Security and Operations. DevSecOPs brings together best practices to implement security in all stages of the SDLC. Cybersecurity on the other hand extends to different domains such as planning, designing, implementing security for architecture, network and applications.
2. What is the difference between DevSecOps and Agile?
Agile is focused on adaptability in the development process whereas DevSecOps is all about development with emphasis on security. DevSecOps underscores the importance of incorporating security during the development process. While DevSecOps deals with security right from the beginning, Agile development techniques introduce security to applications at the later stages.
Ready to protect your app?
Start 30-days FREE TRIAL. No credit card required. Deliver Secure Mobile Apps Faster in minutes with the leader in application security.