Applications deployed in enterprises sit in a complex and fragmented environment in a mélange of networks, operating systems, and databases. This often leads to fragmentation in the application’s security architecture, coupled with a lack of precise and fool-proof security road map.
Instead of addressing the design flaws in apps, developers tend to adopt static and traditional AppSec approaches, which often fail in the light of complex security threats. Such disparate layers of security control often become a bottleneck for multiple components at the application, infrastructure, and security layers, but with the arrival of RASP security solutions, app security is no longer a casual reaction to threats. The concept of runtime application self-protection or RASP security has been developed largely to address the ad-hoc approaches adopted by developers when they come face to face with threats.
RASP Security (Runtime Application Self-Protection)
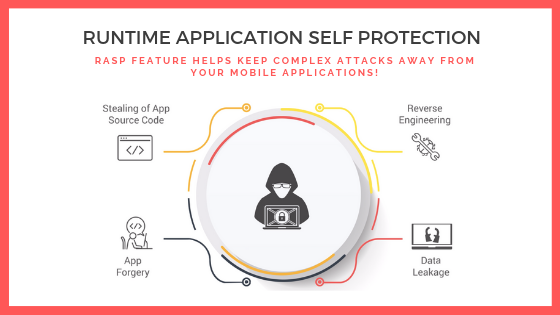
Runtime application self-protection (RASP) is an innovation in the application security ecosystem equipped to deal with runtime attacks on the software’s application layer by providing more visibility into hidden vulnerabilities. It is essentially a security software that integrates with an application or its runtime environment and constantly intercepts calls to the application to check their security. A RASP security software does not wait for a threat to impact the app. Instead, it proactively hunts for malware in the incoming traffic to the app and prevents fraudulent calls from executing inside the app.
How does RASP Security Work?
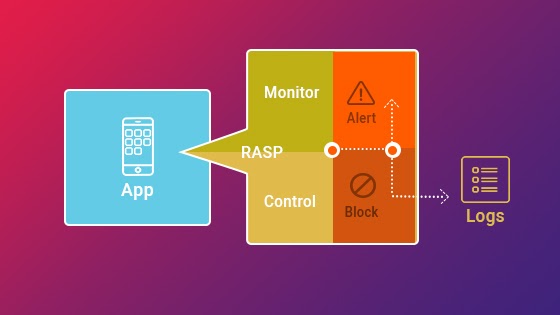
RASP technology is a server-based technology that activates as soon as the application runtime begins. This means that RASP can be triggered by integrating function calls inside the app’s source code or using an external coat on a completed app to trigger RASP with a single command. However, most developers prefer using trigger calls within the code-base as it allows them to construct a customized security system based on the business requirements. With this method, you can precisely determine the protection parameters and optimize the runtime by avoiding unnecessary security checks.
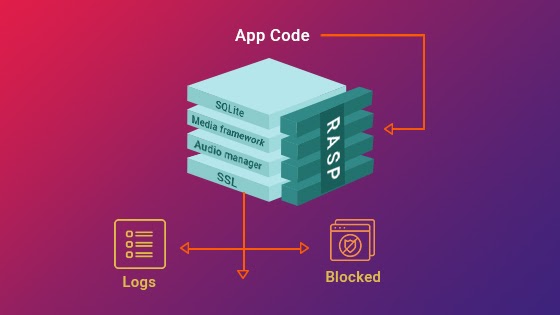
A RASP layer sits side-by-side with the application code and monitors the incoming traffic to the server and APIs of the application. Upon detecting any threat vectors, RASP applies runtime protection measures and secures the application from malpractices. All requests are vetted through the RASP layer sitting between the application and the server, without impacting the app’s performance.
RASP has powerful capabilities to not only detect threat vectors – just like WAF – but to initiate actions to counteract the damages which can occur if the threat is allowed to be executed. Depending on the implementation, this could mean simply terminating a user session or analyzing traffic at runtime and monitoring vulnerabilities for their impact on the application. Due to its proximity to vulnerable code inside the application, RASP triggers fewer false positives.
RASP Vs WAF
A traditional security approach, like a web application firewall (WAF), normally sits in front of web applications, inspecting incoming HTTP request traffic for known attack payloads and abnormal usage patterns. WAF works well only in situations where an attack is known, for which firewall rules can be built in WAF.
But, for emerging threats, it becomes ineffective since developers cannot write rules for blocking them. On the other hand, RASP integrates within the app to not only detect threat vectors but also initiate measures to block them. By staying within the application, a RASP solution neutralizes known vulnerabilities and protects apps against unknown zero-day attacks without needing any human intervention. Hence, RASP offers a conceptually different security paradigm than traditional security approaches like web application firewalls (WAF), which protect an app simply by blocking all suspect traffic.
Benefits of RASP Security
The biggest benefit of RASP technology is that it works from inside the application, rather than remaining as an isolated network protection method, like a firewall. This characteristic allows RASP to provide a contextualized service – taking necessary information from the codebase, APIs, system configuration, runtime data, logic flow, etc.
Intelligent Penetration Testing:
With RASP technology, you can conduct effective penetration testing to detect and eliminate vulnerabilities. As mentioned earlier, the software can be designed to detect anomalies and respond accordingly. You can also easily reprogram and test different sections conveniently.
Smarter Incident Response:
RASP technology enables smarter and faster incident response. Due to the in-depth visibility into the application runtime and the active security logging features, developers get real-time data of the behavior within the application. This further empowers the monitoring capabilities, allowing developers to render more effective security designs.
Visibility into Runtime Attack:
Traditionally, developers couldnt collect runtime application security data, so the security structure had to be designed on the basis of speculations and guesses. A lot of it changes with the integration of RASP software. RASP empowers developers with extensive visibility into the application runtime security events, allowing them to align the development with the real-time events more precisely.
Supports Compliance Development:
Apart from providing security, RASP technology greatly supports the development aspect of applications. With in-depth testing and real-time data, developers can effortlessly identify the prime attack assets and vulnerabilities. This allows them to develop more secure and compliant applications with fewer vulnerabilities every time.
Legacy Application Protection:
A legacy application is a valuable asset for an enterprise. However, with modern advancements, protecting legacy applications is not easy. Most legacy apps are developed in older formats, making it difficult to render security against modern threats. RASP technology solves this issue and allows you to wrap the legacy app with advanced security features without the need to touch the existing code-base.
Added Layer of Protection:
When coupled with the existing WAF and IPS security setups, RASP acts as an added layer of protection that further improves security and reduces vulnerabilities. While the firewall protects the app from incoming threats, the RASP technology actively monitors the runtime and eliminates threats within the app.
Self-Protection:
Once deployed, RASP acts as an independent security system that detects and eliminates threats with minimal human intervention. Therefore, providing a self-protecting application
runtime, where the application protects itself and rewards you with precise security events and runtime data.
Cost-Effective:
RASP is a highly cost-effective solution considering the amount of security it offers. It is a low-maintenance technology that protects your applications from threats and actively provides
logs of security events. So you get better protection, analytics, and development benefits, all in one package.
Better Developer Training:
Developer training is an integral part of any security team as it greatly reduces the vulnerabilities in application development. With the active use of RASP data, you can feed more precise information about vulnerabilities and attack-prone areas within the application structure. Thus, enabling better application security development in future programs.
Lower false positives
A RASP application has deep insight into the internals of the application, including the capability to see how potential attacks impact the process. The RASP is now able to distinguish between false positives and true attacks (which have a real negative impact on performance and security). By reducing false positives, security teams can spend more time focusing on actual threats.
Zero-day protection
Despite being capable of detecting attacks based on signatures, RASP is not limited to that method. A zero-day attack can be detected and blocked by RASP by identifying anomalous behaviors within the protected application.
DevSecOps Friendly
CI/CD pipelines for DevOps should integrate RASP solutions seamlessly. For increased security across development and deployment, this aligns with DevSecOps practices.
RASP Use Cases
Since RASP is flexible, it can be integrated with a wide range of applications. Some common uses of it are as follows –
Protection of Web Application
An organization’s infrastructure relies heavily on web applications and APIs; however, they are vulnerable to many types of attacks. They are frequently susceptible to exploitable vulnerabilities since they are exposed to the Internet. An organization can reduce its web-facing infrastructure’s cybersecurity risk by deploying RASP to protect these applications and APIs.
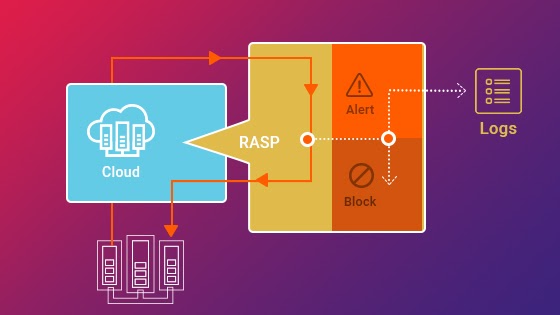
Cloud Application Protection
It can be difficult to keep the cloud secure since applications are run on leased infrastructure outside of a corporation’s firewall. By integrating RASP into these applications, higher levels of security are provided in a portable, infrastructure-agnostic manner.
Zero-day Prevention
The effectiveness of patches is dependent on when they are applied, even when there are processes for applying them swiftly. Utilize RASP to protect application zero-day vulnerabilities, including those in web apps and APIs.
RASP Security Deployment Modes
RASP usually comes in the following modes and can be deployed in any one of them based on requirements:
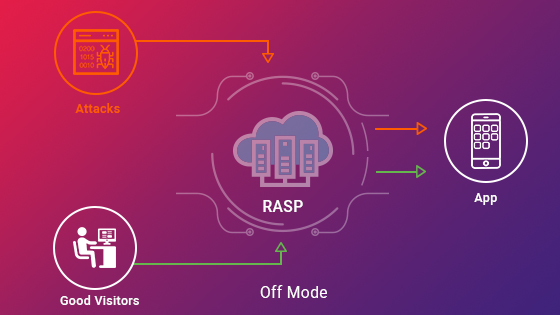
- off mode, which offers neither monitoring nor blocking of calls. Here, all requests are simply passed on without any measures made by the RASP solution.
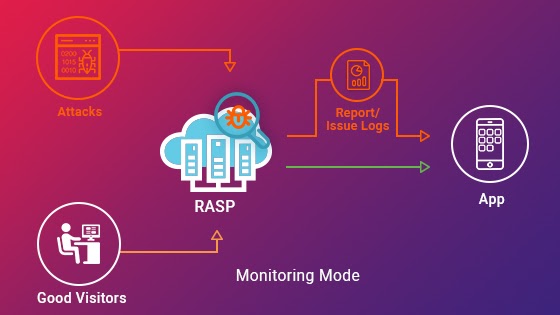
- monitoring/diagnostic mode, where a RASP program monitors the application for threats, records logs, and issues alerts, but does not block requests;
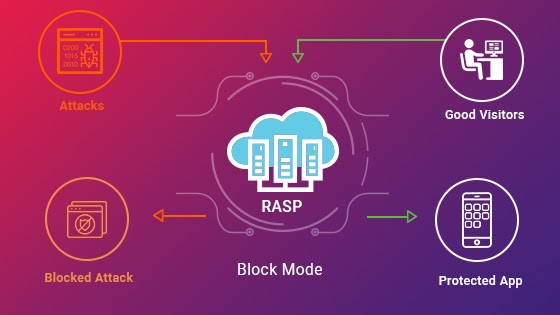
- block mode, where the RASP program goes one step ahead and blocks all illegitimate requests;
- block at perimeter mode, similar to block mode, except here there are certain predefined rules and required actions specified for the RASP solution to thwart attacks even before they are processed by the application. If the attack vector does not match the specified rules, the RASP solution reports it and blocks the same. In this mode, a RASP program behaves like a WAF.
RASP Security Approaches
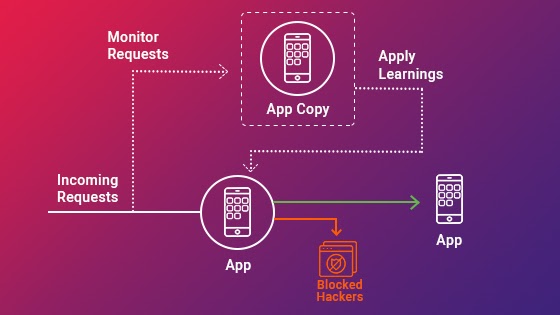
RASP has evolved into a mature concept of in-app security, which has allowed developers to approach neutralizing threats in multiple ways. Depending upon how the developer wants to implement the RASP security layer in the app or the server, they use one of the following four methods:
Servlet filters, SDKs and plugins are implemented into Apache Tomcat or webserver to monitor and inspect incoming HTTP requests and data payloads before they reach the application code. Those resembling vulnerabilities are blocked and, based upon the deployment mode, RASP takes corrective action.
Binary instrumentation includes building monitoring and control elements into the application, with the former identifying security events in the running application, while the latter records such events’ logs and blocks them.
JVM replacement includes replacing the standard libraries – JAR or JVM (in case of Java) – with a RASP layer, which listens to calls made to supporting libraries and applies rules as the calls are intercepted. RASP, thus, has an overall view of app codebase and the system calls routing framework, which enables RASP to learn about machine behavior and sequence flows through passive monitoring of application calls.
Virtualization, also known as containerized runtime protection, creates an application copy and instruments application’s behavior at runtime on the copy by using rules to govern how an application is protected. RASP monitors and learns from app code pathways, logical constructs, parameterization and outputs generated, etc, which is then applied to application requests. This helps in distinguishing between legible requests from malicious ones and allows for appropriate remedial action.
What Should You Consider While Selecting a RASP Solution?
Developers should choose a RASP solution carefully, weighing it on the following parameters:
- It should be easily deployable and require the least maintenance, otherwise, it can become ineffective when the nature of threats change
- It should have a fairly broad capability to detect and handle a huge range of vulnerabilities, both traditional and unknown
- It should have minimal impact on the application’s performance metrics, without which a security layer loses all meaning. No developer will trade users’ comfort for an extra security feature
- A RASP solution should be accurate with least false positives, so as not to block genuine user traffic
- It should work seamlessly with other security tools, like WAF
- It should offer support for multiple frameworks and languages
- A RASP solution must be autonomous, provide support for cloud analysis with round-the-clock monitoring, and block malignant requests
- Above all, it should provide a comprehensive and actionable report on all runtime threats handled and learn from the application’s runtime behavior to protect it dynamically against both passive and active incidents
Conclusion
In conjunction with AppSec testing and WAF solutions, a RASP security solution can prove to be the game-changer your organization needs to quickly and effectively deal with a sophisticated threat landscape. With monitoring, traffic analysis, and learning capabilities of RASP, applications can be equipped with a RASP layer that has capabilities to thwart attacks with high accuracy. RASP’s seamless, no-code deployment and integration also leads to minimal impact on the app’s overall performance, thus making it a must-have security solution.
Going beyond traditional security approaches; Leverage RASP for faster, cost-effective in-app protection.