Modern mobile applications are prone to various threats and the surge in hacking incidents serves as a testament to the need to level up security. Securing apps is becoming tougher day by day since they are run on different devices and operating systems which are beyond the control of the app developer. Safeguarding apps irrespective of the environment they are operating in is a challenge which can be effectively dealt with app shielding.
App Shielding
App shielding is a critical security measure that makes the app resistant to intrusion. In simple words, it blocks attack attempts and saves enterprises from the adverse outcomes of security breaches. App shielding makes it difficult for hackers to penetrate and initiate attacks. It relies on a series of techniques to prevent code manipulation attempts and close similar security gaps.
Application shielding takes a proactive stance and prevents attacks, rather than simply reacting to the attack. And at a time when mobile applications are more prone to attacks than ever before, app shielding can prove to be a critical defense mechanism against data breaches and risks to confidentiality that could lead to a damaged reputation and lost customer confidence. This article discusses app shielding and its importance at length.
Apps are highly convenient to use and no business wants to miss the opportunity to offer easier access and better connect with customers. However, with the growing use of apps, it is a fact that hackers are on the rise to make the most of the opportunity and steal data. This is especially true for banking and financial services applications where there is an exchange of sensitive information.
Data breaches have exposed an estimated 36 billion+ records in the first half of 2020.
This statistic is enough to explain how app shielding is no longer a choice but a necessity. App shielding complicates the process of reverse engineering for hackers thereby increasing the resistance of applications to withstand any attempts of unauthorized access. It is a solid remedy to protect intellectual property and counter piracy.
Importance of App Shielding
App shielding is crucial for any organization that doesn’t want to compromise security, risk data integrity and fall prey to attacks time and again, which is basically every business in existence. Here are a few solid reasons to invest time and efforts in app shielding:
- Over 67% of financial institutions have confirmed an increase in cyber attacks leading to credential leaks. App shielding protects business reputation by minimizing risks of sophisticated, highly targeted attacks.
- Mobile channels are the main target of fraudsters. Risks associated with mobile apps are increasing and app shielding is of utmost importance to keep up with the evolving landscape of security vulnerabilities and attacks.
- Finance and healthcare organizations must never function without app shielding. It is a must-have security measure since a single breach can result in losing customers permanently to competitors.
- App shielding protects data and intellectual property by making the apps resilient against runtime attacks.
- App shielding facilitates secure enabling of certain features that may otherwise pose a threat thereby presenting an opportunity for revenue growth.
For those who are determined to gain a competitive edge in this security compromised app industry, app shielding is the way to gain trust and get ahead of the race.
How Does App Shielding Work?
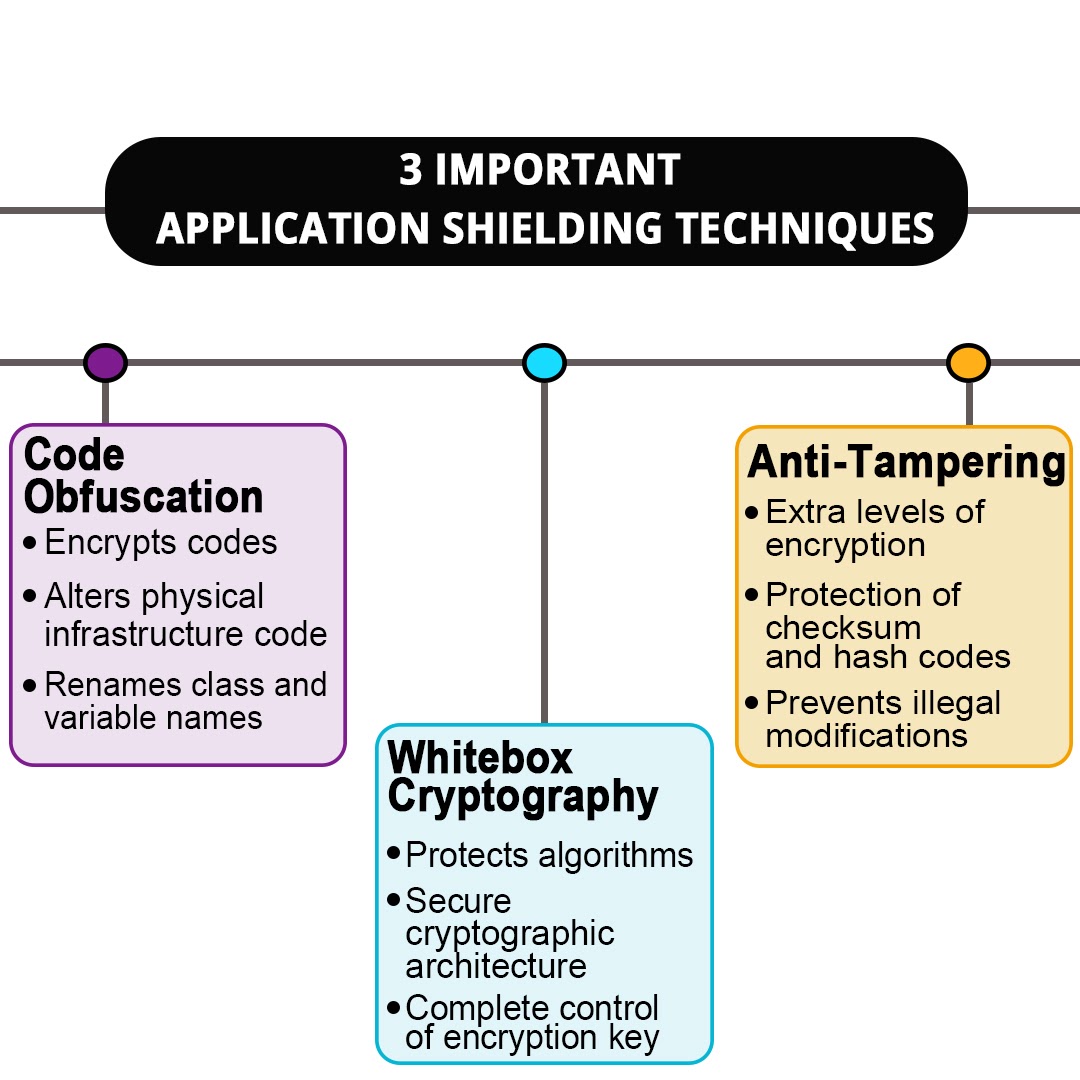
App shielding levels up security through code obfuscation, white box cryptography, and anti-tampering. We will deep dive into understanding how each of these contributes to app protection.
Code Obfuscation
Code obfuscation is done to protect IP and prevent attackers from reverse engineering. The code is altered in such a way that the behavior of the app remains unchanged. But at the same time, it confuses the hackers. Codes are encrypted, revealing meta data is removed and the application binary is populated with irrelevant codes along with renaming useful class and variable names. Apart from these methods, developers tend to manipulate code to make it difficult for potential attackers to keep track without making any structural changes to the app.
Whitebox Cryptography
Sensitive data remains stored in the device which can be easily misused. Whitebox cryptography successfully protects and hides encryption keys. Exposed encryption keys are an opportunity for hackers to launch an attack. Whitebox cryptography generates a unique cryptographic architecture and conceals the algorithms to keep them from appearing clearly in the memory of the device and protect critical application data. The process makes it hard for any potential attacker to find the original key despite the cryptographic algorithms being available and open to modification. White-boxing techniques are similar to obfuscation but may also use additional anti-tampering methods to derive the desired result.
Anti-tampering
Anti tampering prevents the hackers from figuring out the decryption method that wins them access to the software. It uses obfuscation but goes one step further by adding an extra layer of security making it difficult for the hacker to decode the encryption. It effectively hides checksum and hash codes to counter illegal modifications to the application.
App Shielding Benefits?
App shielding has a host of benefits owing to its prevention, detection, and response capabilities. Mobile apps must effectively thwart attacks while never compromising on user experience. The top benefits of app shielding are outlined below.
User Experience
There are chances that the app may be downloaded into a jailbroken or rooted device. This implies that the default security layers of the operating system have been compromised. The environment in which the app operates may itself emerge as a threat. App shielding, nevertheless, insulates the app against malware lurking in the device and offers uninterrupted service to customers.
Multilayered Protection
App shielding offers multi-layered protection by securing the app against a variety of threats like overlay attacks, keyloggers, screen readers, code injection among others. Cyber criminals rely on a series of tools like emulators, debuggers, hooking frameworks among others to breach security and app shielding wraps around the application to form a protective shield.
Compliance with Regulations
App shielding helps comply with PSD2, FFIEC and GDPR regulations. These are security standards that govern the safety of online payments and data exchange. Customizable app shielding solutions from a reputed security solution provider can meet the compliance requirements of different businesses in different countries.
Supports DevSecOps
DevSecOps means integrating security right from the start rather than treating it as a separate perimeter that works around apps. App shielding seamlessly integrates into the application development pipeline which ultimately accelerates the speed to market and leads to rapid and frequent development cycles
It is necessary to choose the best app shielding solution to avail all the above mentioned benefits and more. The best way to ensure top-notch security is to seek app shielding solutions from a security solution provider with proven expertise in catering to diverse industries.
Choosing an Appropriate App Shielding Solution for Apps
An app shielding solution must possess certain features to guarantee desired levels of security in this evolving mobile threat landscape where malicious actors are constantly launching sophisticated attacks. Here are a few tips to choose an app shielding solution that works under extreme conditions to counter actual cyber threats.
Low Level Implementation in Native Module
Though code obfuscation offers protection, it is not enough given the current state of cybercrime activities. The most determined hacker can penetrate through code obfuscation. To counter this, the app shielding solution must be implemented in the native module using C or C++. Codes in high-level mobile programming languages are not recommended as it results in weak runtime resilience and poor memory management. An app shielding solution must integrate into the app as a native library with codes written in C or C++ for better resistance against reverse engineering, runtime tampering and superior performance.
Automated Implementation
Launching an SDK manually as a part of app shielding is a failed attempt to secure apps. With automated app bundle processing, one can modify the app bundle during or after build time. The app protection is live before the app completes its loading process thereby preventing any malicious activity from tampering with the app. Choose an app shielding solution that can be plugged in with no codes through automation. Implementing app shielding through programming is not a security best practice for DevSecOps initiatives.
Exclusion of Some Users Under Certain Conditions
App shielding deployment may not work in some cases which may lead to exclusion of some users. A solution provider that claims app shielding will offer protection under all circumstances is probably not aware of how app shielding works. Some devices are heavily modified due to jailbreak, active injection scripts, and several such factors. A shielded app in such a device will cause the app to terminate. Choose an app shielding solution provider that clearly defines the cases under which the end users may be impacted.
Selecting the right app shielding solution is crucial since it determines how well your application withstands hack attempts and performs with zero compromise on user experience.
Final Thoughts
App shielding is a powerful security solution that speeds up pen-testing efforts and reduces time-to-market. It meets the rigorous security requirements by tackling screen monitoring, code injection, emulators, screen readers, jailbreak/rooted devices, overlay attack, repackaging, screenshots, keylogging, and debuggers.
Key Takeaways:
- App security may be compromised due to corruption of the execution environment, reverse engineering or duplication of apps and modified and repackaged apps published in alternative app stores.
- App shielding is necessary not just to pass annual security audit reports but to prevent losses due to poor brand image resulting from repeated attacks.
- App shielding relies on code obfuscation, white box cryptography and anti-tampering to proactively shield the app from intrusions.
- It secures all the components of the app and enables the introduction of new features.
- Special attention must be paid to choosing an app shielding solution.
- An app shielding solution that can be added automatically with no code during the build process or CI/CD pipeline is preferable.
- An automated implementation process is necessary when you have to release multiple secured apps without affecting the development timeline.
Appsealing is a scalable security solution that offers excellent compatibility with third-party tools like Jenkins, TeamCity, Crashlytics. Designed to function without coding, it not only thwarts attacks but captures data on all hacking attempts to help iOS and Android app developers make better informed decisions. With deep lying expertise in delivering security solutions across industries like gaming, fintech, O2O, movies, eCommerce, and public sector applications, Appsealing guards your brand image with patented solutions and technology that never compromises app performance or user experience. Get in touch with us today to discuss your requirements or to learn more about our services