Developers around the world know that not every app security – AppSec in tech lingo – initiative can be a resounding success. But, more often than not, experience gained from undertaking such initiatives helps developers make robust applications in future. Let us deep dive into six such mistakes which businesses and developers usually commit while implementing AppSec measures. Inheriting certain best practices from such mistakes helps businesses in evolving a robust security road map in the face of ever-increasing cyber threats. These measures should be implemented in due course to stay ahead of the curve in a rapidly evolving threat landscape.
One such oft-repeated mistake is associated with inadequate testing of applications. Developers/testers usually execute a limited set of testing techniques on the application, without thinking through the necessity and applicability of each testing type. This is determined by the stage in which the application is currently in, as well as overall AppSec requirements. With secure software development life cycle (sSDLC) ruling the roost, both static and dynamic analysis are required to have an effective, comprehensive AppSec testing methodology.
Complementary World of Static and Dynamic Analyses
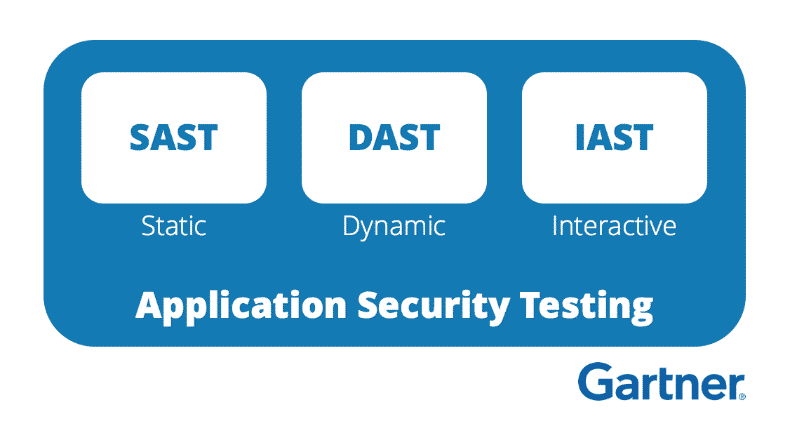
Static application security testing (SAST) is essentially white-box testing, through which developers get to know the architecture and source code of the application. Hence, SAST helps in inspecting codebase to find flaws and malware in a non-runtime environment. With increasing reports of website vulnerabilities and data breaches at deployment level, it has become indispensable to test deployment configuration for security vulnerabilities, like cross-site scripting. On the other hand, dynamic application security testing (DAST), also knows as black-box testing, is executed on the run-time environment and helps in monitoring overall application performance. Since DAST can only be implemented only in the live situation, it cannot examine the source code of the app.
 Image Credit- Gartner Application Security terms SAST, DAST, and IAST
Image Credit- Gartner Application Security terms SAST, DAST, and IAST
As noted above, both static and dynamic analysis complement each other, and one method’s weaknesses becomes another method’s strength. Static analysis cannot identify issues arising from encapsulation, deployment configuration, cross site scripting, etc. In fact, with the advent of agile development model and quick sprints becoming the order of the day, the changes effected in the application require thorough and comprehensive testing. Static analysis, due to its white-box approach, is more cost efficient in identifying security threats in early stages of software development and effective in unearthing future bugs in the system.
Read More about- Protect applications against OWASP TOP 10 Mobile Application Risks
Dynamic analysis, on the other hand, complements static analysis in exposing flaws which can go undetected until the app hits the production stage. After the application build is complete and ready for deployment, the executed code is tested using dynamic analysis. Though not ideal in the case of continuous-integration-continuous-deployment (CICD) projects – because if the app code is frequently updated, its runtime evaluation becomes difficult – still it is essential to assess security throughout an application’s life cycle, starting from inception till production.
Synergizing Security Strategies
Static analysis checks your application inside-out by examining the app’s codebase and its binaries for any security vulnerabilities, whereas dynamic analysis examines the application outside-in while the application is in execution mode. This results in both forming a complete testing methodology. Leaving out one does leave possible attack vectors untested and the application vulnerable to security threats.
Formulating a security strategy requires developers/testers to implement a planned testing strategy to assess both server-side and client-side vulnerabilities. This helps the development team in blending the security framework with latest development models, like CICD, Agile and DevOps. In addition to using automated security testing tools, manual intervention is also necessary to exploit, verify, and properly patch the vulnerabilities.
Read more about- Vulnerability Scanning and Penetration Testing: Two Complementary Approaches to App Security
Gone are the days when hackers used simple techniques, like phishing, to fleece the user. Now, their options to inject malicious codes in an app have increased and, therefore, forced developers to create foolproof testing methods for their apps. Hence, it can be concluded that there is no single panacea to exploit an application to detect all security threats in one go. Neither static nor dynamic analysis alone can offer a hundred percent threat detection. The development/testing team should bring about a synergy between both these techniques and implement them to evolve a future-proof security solution, which is a common omission developers make when hard-pressed to meet tight deadlines in a continuous version upgrade cycle.
Checkout our article on AppSec Mistakes Part-2 where we will help you understand the threat of open source libraries and how to overcome it.
Talk to our experts about your security issues at support@appsealing.com